2015-12-31
[public] 18.4K views, 393 likes, 9.00 dislikes audio only
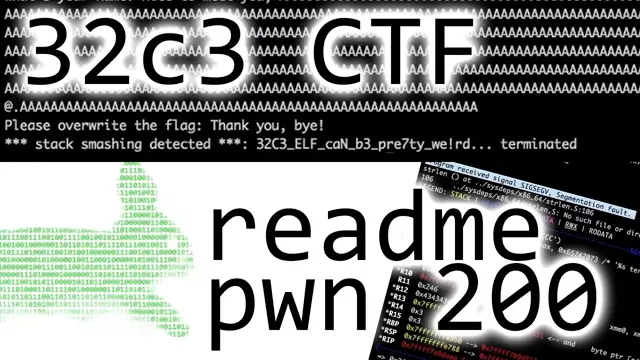
Solving the readme pwnable 200 from the 32c3 ctf. I didn't solve it during the CTF but worked through several writeups and doing some more research. Now that I understood it I recorded solving the challenge again and recorded a commentary for it.
CORRECTION: I explained the stack canary with the `fs` register wrong. The `fs` register has an address and the stack canary is stored at offset +0x28 from that address.
Stack Layout for an ELF program: https://www.win.tue.nl/~aeb/linux/hh/stack-layout.html
Credits: https://github.com/ctfs/write-ups-2015/tree/master/32c3-ctf-2015/pwn/readme-200
Vagrant: https://www.vagrantup.com/
CTF VM: https://github.com/thebarbershopper/ctf-vagrant-64
BinaryNinja: https://binary.ninja
-=[ 🔴 Stuff I use ]=-
→ Microphone:* https://geni.us/ntg3b
→ Graphics tablet:* https://geni.us/wacom-intuos
→ Camera#1 for streaming:* https://geni.us/sony-camera
→ Lens for streaming:* https://geni.us/sony-lense
→ Connect Camera#1 to PC:* https://geni.us/cam-link
→ Keyboard:* https://geni.us/mech-keyboard
→ Old Microphone:* https://geni.us/mic-at2020usb
US Store Front:* https://www.amazon.com/shop/liveoverflow
-=[ ❤️ Support ]=-
→ per Video: https://www.patreon.com/join/liveoverflow
→ per Month: https://www.youtube.com/channel/UClcE-kVhqyiHCcjYwcpfj9w/join
-=[ 🐕 Social ]=-
→ Twitter: https://twitter.com/LiveOverflow/
→ Website: https://liveoverflow.com/
→ Subreddit: https://www.reddit.com/r/LiveOverflow/
→ Facebook: https://www.facebook.com/LiveOverflow/
-=[ 📄 P.S. ]=-
All links with "*" are affiliate links.
LiveOverflow / Security Flag GmbH is part of the Amazon Affiliate Partner Programm.
#CTF #BufferOverflow #BinaryExploitation
/youtube/video/wLsckMfScOg?t=240
/youtube/video/wLsckMfScOg?t=300
/youtube/video/wLsckMfScOg?t=860
/youtube/video/wLsckMfScOg?t=894
/youtube/video/wLsckMfScOg?t=970
/youtube/video/wLsckMfScOg?t=1286
/youtube/video/wLsckMfScOg?t=1542
/youtube/video/wLsckMfScOg?t=1600
/youtube/video/wLsckMfScOg?t=1638
/youtube/video/wLsckMfScOg?t=1703